
Before founding software-defined networking startup PlumGrid and then moving to VMware when it bought his company in 2016, Pere Monclus spent almost 12 years with Cisco Systems at a time when while much of enterprise networking was still in the corporate datacenter, the shift to network virtualization and the migration to the cloud were getting underway.
Cisco was dominant in the datacenter networking space and fed organizations with a steady stream of hardware, from routers to switches to silicon. The company carried an expansion view of its role in networking.
“At Cisco, we were thinking always we have to control the end-to-end of the network,” Monclus, vice president and chief technology officer of VMware’s Networking and Security business unit, tells The Next Platform. “The idea was we have to control the edge of the network so the core doesn’t fall, because the core was where most of the markets were. We would have core routers, core switches and then take it all the way to the access to create the end-to-end networking as a principle, because from a Cisco perspective, what we were delivering was an end-to-end connectivity solution with our protocols.”
About a year after Monclus left Cisco to found PlumGrid, VMware bought Nicira for $1.26 billion, a move that allowed the company that already was a significant datacenter presence through its server and storage virtualization to absorb networking into its increasingly software-defined world. NSX and networking have evolved over the past ten years to become a key part of VMware’s own adaptation to an IT world that has broken well beyond the datacenter boundaries and out to the cloud and the edge. With containers, microservices and Kubernetes, software now dictates to hardware rather than the other way around.

It’s also a world where the network is now tie that binds this increasingly decentralized IT environment, becoming the main thoroughfare for applications and data moving between the datacenter, cloud and edge and a central focus for organization’s security measures. All this was on full display this week at VMware’s Explore 2022 conference, which allowed the company to tout its ongoing expansion into the cloud and out to the edge and its networking portfolio’s central role in helping to make this happen.
The evolution of networking at VMware has taken several steps, Monclus says. At the time of the Nicira acquisition, enterprises would spend weeks or months putting the network in place before applications that would run top it could be put into production.
When VMware got into networking, the company heard from customers that they could quickly create and application and get a server up and running, “but it takes them weeks to configure the network,” he says. “We started that journey with network virtualization and the first story [for networking] was about automation and agility. The question was, ‘If I create a VM, could I just connect it to the network and give it an IP address?’ That was kind of the early days of network virtualization.”
As more workloads and data were making their way out of the datacenter, security of the network became increasingly important, which is why VMware embraced micro-segmentation, a way to manage network access and separate workloads from one another to reduce an organization’s attack surface and more easily contain breaches by preventing the lateral movement of attackers. The acquisition two years ago of network security startup Lastline helped fuel the vendor’s distributed IDS/IPS technology to complement the east-west protection delivered by micro-segmentation.
In June, the company added to its lateral security for network and endpoint technologies with a broad threat intelligence capability called Contexa. It sits in the infrastructure and offers visibility into both traditional and modern applications.
VMware over the years has put networking and security capabilities into the hypervisor and made them available as services in its own cloud offering and those of hyperscalers like Amazon Web Services and Google Cloud. It’s also making NSX, and its expanding growing security capabilities – including those from Carbon Black, which it bought in 2019 for $2.1 billion –key parts of the multicloud strategy.
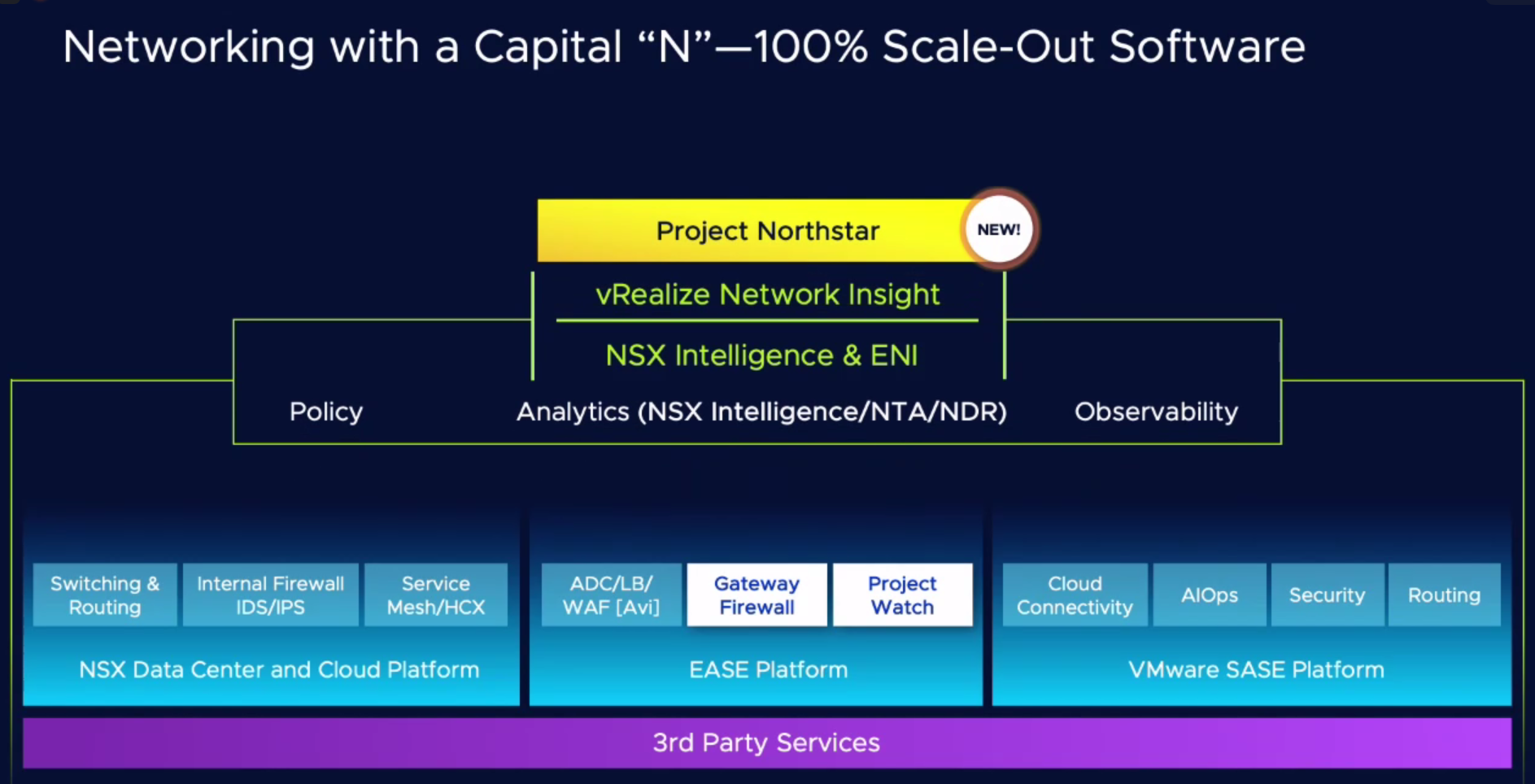
The vendor at Explore rolled out a broad range of enhancements to its networking and security portfolio all aimed at making it easier for enterprises to manage and secure their multicloud environments. It also gave a look to what the near-term future looks like with the introduction of a number of network- and security-focused projects.
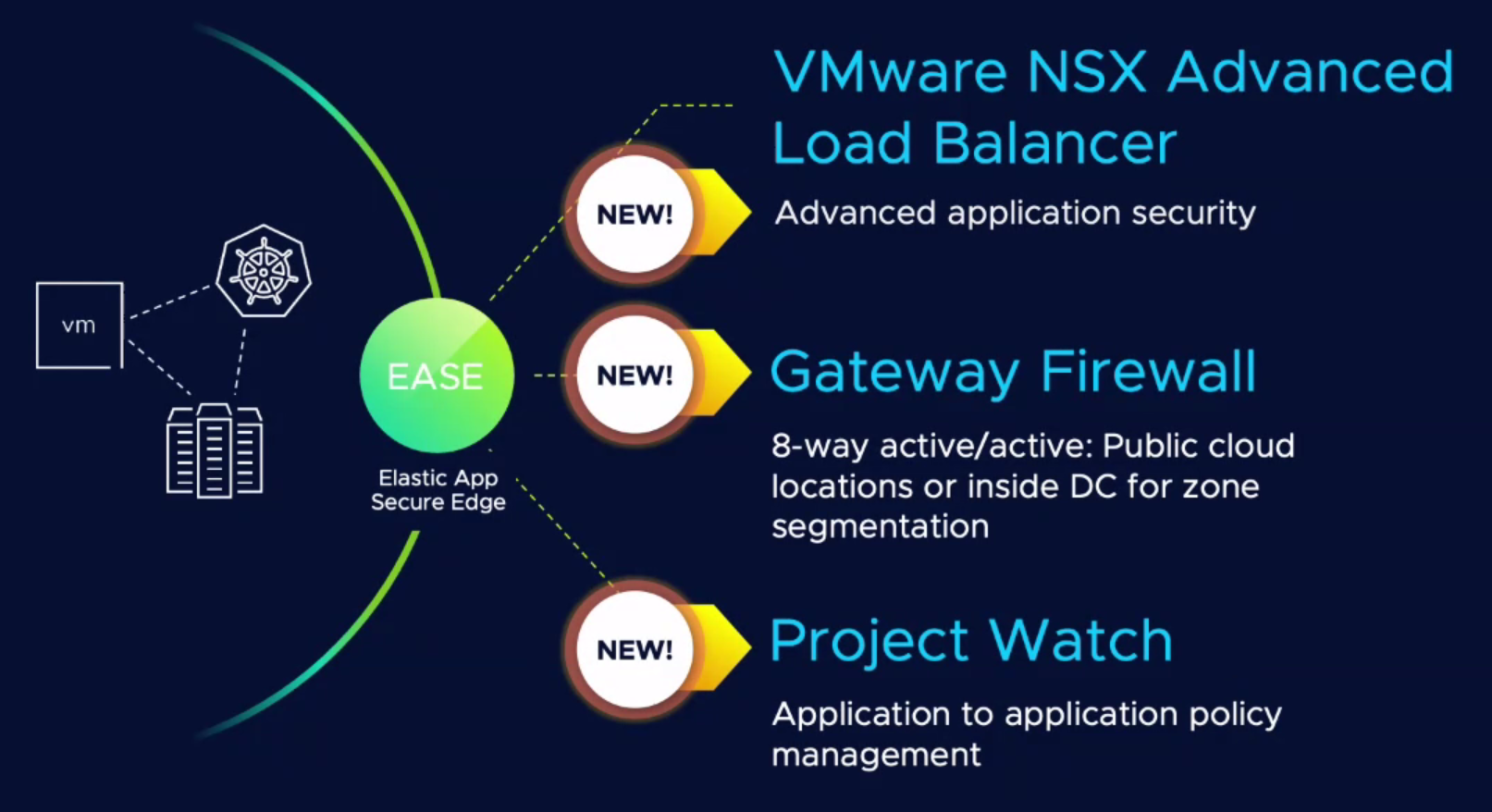
VMware is embedding network detection and visibility capabilities into Carbon Black Cloud’s endpoint protection program, a move that is now in early access and brings together visibility into both the network and endpoints. It also is adding threat prevention tools like IDPS, malware analysis, sandboxing and URL filtering to its NSX Gateway Firewall and enhanced bot management to the NSX Advanced Load Balancer (ALB). The last two – along with Project Watch, which aims to offer a continuous risk and compliance assessment model to multicloud environments – are part of VMware’s Elastic App Secure Edge (EASE), a strategy announced last year to offer a range of data plane services around networking and security.
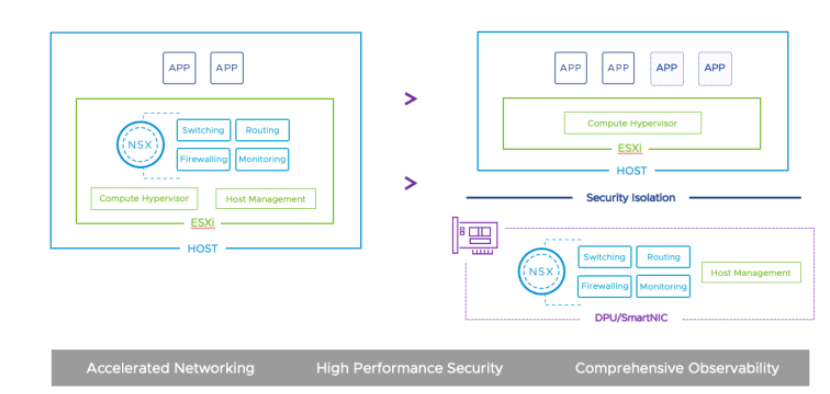
As we noted earlier this week, VMware also is embracing data processing units (DPUs) from Nvidia for a number of its cloud-based offerings, including vSphere 8 and, for this case, NSX. Cloud providers like AWS and Oracle already are using DPUs and many in the industry believe that servers and other hardware in the near future will routinely include the chips. Monclus says customers that will gravitate toward DPUs – or smartNICs – for performance and security. For organizations like telcos that demand high performance – and where their datacenters are revenue-generating facilities – enabling CPUs to offload networking or compute tasks to DPUs is attractive.
There is a tradeoff – they may save 15 percent in CPU utilization, which they can sell back to customers, but there also is the cost of the DPUs themselves. However, where datacenters are a cost factor, increasing security by leveraging the workload isolation offered by the DPUs and that likely will be a fast-growing use case for the chips, Monclus says.
Looking to the near future, VMware offered a look at Project Northstar and Project Trinidad, along with the aforementioned Project Watch. Project NorthStar is in technical preview and is a software-as-a-service (SaaS) network and security offering that will deliver services, visibility and controls to NSX users who can manage them via central cloud control plane.
The services include VMware’s NSX Intelligence, ALB, Network Detection and Response and Web Application Firewall.
“We are taking the control plane of NSX and turning it into a SaaS service to enable true multicloud solutions,” Monclus says. “When we have a policy as a service, it works on vSphere environments but it works across VMware Cloud, VMware Cloud Network, AWS, Google, Azure, and we have the same advanced protection, we have the same load balancer.”
Both Project Trinidad and Project Watch are aimed at addressing the needs of modern workloads, he says. They’re not tied to physical endpoints; instead, the API becomes the endpoint, he says. Project Trinidad uses AI and machine learning models to understand what are normal and expected east-west API traffic patterns between microservices so that if something anomalous pops up, it can be quickly detected.
“We basically discover all the API, the schemas, API data and we create a baseline and we can start from the baseline,” Monclus says. “Project Trinidad introduces is AI/ML deep correlations between workflows and microservices.”
As noted, Project Watch brings continuous security, compliance and risk assessment as well as automated and encrypted connectivity across clouds – AWS, Google Cloud and Microsoft Azure – virtual private clouds (VPCs) and virtual networks (VNETs) and security operations and integrates workflows from such areas as security and cloud operations and lines of business onto a single platform.
It also addresses the challenge of not only enabling networks and security to adapt to modern workloads but also to ensure that legacy hardware that can’t make that change are secure.
VMware will assess and report the security risks enterprises face, giving the necessary data to make decisions, he says, adding that the vendor wants “to create a continuous monitoring model in the same way as high availability, which uses the metric of three 9s, four 9s, and so forth,” he says. “We are trying to create a metric of how well you’re running your datacenter or your applications from across security points.”




Be the first to comment